In today’s digital landscape, where cyber threats are becoming increasingly sophisticated, traditional security measures are no longer enough to protect sensitive information. This has led to the rise of the Zero Trust architecture, a security framework that focuses on maintaining strict access control and constant verification of users and devices, regardless of their location. The implementation of Zero Trust architecture requires a combination of different technologies to ensure a robust and effective security system. In this blog post, we will discuss the key technologies required for Zero Trust architecture implementation.

At the heart of Zero Trust architecture is the concept of identity and access management. IAM enables organizations to establish and enforce strict access controls by verifying the identity of users and devices before granting them access to resources. This is crucial in a Zero Trust environment where no user or device is automatically trusted. IAM solutions such as multi-factor authentication, bio-metric authentication, and single sign-on are essential in implementing Zero Trust architecture.
Multi-factor authentication (MFA) adds an additional layer of security by requiring users to provide multiple forms of authentication, such as a password, security token, or bio-metric data. This significantly reduces the risk of unauthorized access to sensitive resources, even if a user’s login credentials are compromised. Bio-metric authentication, on the other hand, uses unique physical characteristics like fingerprints or facial recognition to verify a user’s identity. This is a more secure and convenient method of authentication, eliminating the need for passwords.
Single sign-on (SSO) is another critical component of IAM in Zero Trust architecture. SSO allows users to access multiple applications and services using a single set of login credentials. This reduces the number of passwords a user needs to remember, making it easier to manage and more secure.
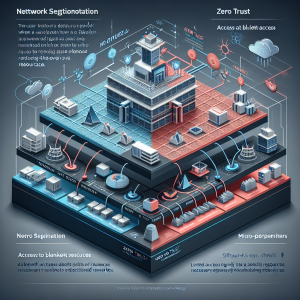
Network segmentation is a fundamental aspect of Zero Trust architecture. It involves dividing a network into smaller, isolated segments to restrict access to sensitive resources. In a traditional network, once a user gains access, they have access to the entire network. However, with Zero Trust, access is restricted to only the segments needed to perform specific tasks. This reduces the risk of lateral movement by cyber-criminals who gain access to the network.
To implement network segmentation, organizations can use virtual local area networks (VLANs) or software-defined networking (SDN). VLANs divide a physical network into logical segments, while SDN uses software to create logical network segments. These technologies allow for the creation of micro-perimeters within a network, limiting access to sensitive resources and reducing the attack surface.

Endpoints, such as laptops, smartphones, and IoT devices, are often the weakest link in an organization’s security posture. This is because they are usually outside the organization’s network perimeter, making them vulnerable to cyber attacks. In a Zero Trust architecture, endpoints must be continuously monitored and verified to ensure they are secure before granting access to sensitive resources.
Endpoint security solutions such as antivirus software, intrusion detection and prevention systems, and data loss prevention tools are crucial in implementing Zero Trust architecture. These tools help identify and mitigate potential threats on endpoints, ensuring they are secure before being granted access to the network.

Encryption is the process of converting plain text into code to prevent unauthorized access to sensitive information. In a Zero Trust environment, data must be encrypted both in transit and at rest to ensure it remains secure. Encryption helps prevent cyber-criminals from intercepting data as it travels across networks or being able to read it if they gain access to it.
Organizations can implement encryption using various technologies, such as virtual private networks (VPNs) and secure sockets layer (SSL) certificates. VPNs create a secure connection between a user’s device and the organization’s network, while SSL certificates encrypt data between a user’s browser and a website. Encryption is a vital component of Zero Trust architecture, as it ensures sensitive data remains secure, even if it falls into the wrong hands.

In a Zero Trust environment, continuous monitoring and analytics are crucial to ensure the security posture remains strong. This involves monitoring user and device activity at all times, detecting any suspicious behavior or anomalies, and taking appropriate action. Continuous monitoring and analytics provide real-time visibility into the network, allowing organizations to respond to potential threats promptly.
This can be achieved using technologies such as security information and event management (SIEM) systems, intrusion detection and prevention systems, and user and entity behavior analytics (UEBA). These tools use machine learning and artificial intelligence algorithms to detect anomalies and potential threats, providing organizations with the ability to respond quickly and effectively.
In conclusion, implementing Zero Trust architecture requires a combination of different technologies to ensure a robust and secure framework. From identity and access management to continuous monitoring and analytics, each component plays a crucial role in creating a secure and trusted environment. By implementing these technologies, organizations can reduce the risk of data breaches and cyber attacks, ensuring their sensitive information remains protected. As cyber threats continue to evolve, the adoption of Zero Trust architecture is becoming increasingly necessary for organizations to maintain a strong security posture.