In recent years, the concept of zero trust has gained traction in the cyber-security world as a way to combat the increasing number of cyber threats. Zero trust is a security framework that assumes no user or device can be trusted, both inside and outside the network perimeter. Instead, it requires strict authentication and authorization for all users, devices, and applications. While the concept of zero trust is relatively simple, implementing it can be a daunting task for many organizations. In this blog post, we will discuss some common challenges in zero trust implementation and how to overcome them.

One of the biggest challenges in implementing a zero trust model is the lack of understanding of what it entails. Many organizations believe that implementing zero trust means simply adding more security layers and controls, but this is not the case. Zero trust is not just about adding more security measures; it is about changing the entire approach to security.
To overcome this challenge, organizations need to educate themselves on what zero trust truly means and how it differs from traditional security models. They should also seek guidance from experts or consultants who can provide a better understanding of the concept and help with the implementation process.
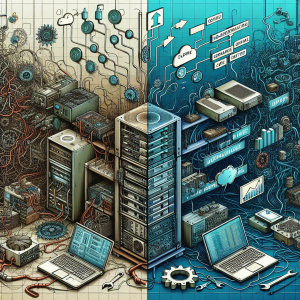
Another common challenge in implementing zero trust is dealing with legacy systems. Many organizations have a complex IT infrastructure with a mix of old and new systems, making it difficult to implement a uniform zero trust model. Legacy systems may not be capable of supporting the necessary security measures, or they may not be compatible with newer technologies.
To overcome this challenge, organizations can start by identifying and prioritizing their legacy systems that need to be replaced or upgraded. They should also consider investing in modernizing their IT infrastructure to support a zero trust model in the long run. In some cases, implementing micro-segmentation, which divides the network into smaller, more manageable segments, can also help in securing legacy systems.

Implementing a zero trust model requires the integration of various security tools and technologies. However, many organizations struggle with integrating these tools and creating a cohesive security system. This can lead to security gaps and vulnerabilities, defeating the purpose of a zero trust model.
To overcome this challenge, organizations should carefully evaluate their existing security tools and determine which ones can be integrated to support a zero trust model. They should also consider investing in a unified security platform that can integrate various tools and provide a centralized view of the security posture.

As with any change, user resistance can be a significant barrier to implementing a zero trust model. Users may find the increased authentication and authorization processes time-consuming and cumbersome, leading to frustration and resistance. This can also result in users finding workarounds to bypass security protocols, creating potential vulnerabilities.
To overcome this challenge, organizations need to communicate the benefits of a zero trust model to their users and provide proper training on how to use the new security measures efficiently. It is also essential to involve users in the implementation process and address their concerns and feedback.

Implementing a zero trust model can be a costly endeavor, especially for small and medium-sized organizations with limited budgets. The initial investment in new security tools, technologies, and infrastructure can be a significant barrier for many organizations.
To overcome this challenge, organizations can start by prioritizing their critical assets and implementing a zero trust model for them first. They can then gradually expand the model to cover other areas. It is also essential to consider the long-term benefits of implementing a zero trust model, such as reduced risk and improved security posture, which can outweigh the initial costs.
Implementing a zero trust model is not an easy task, and organizations are bound to face some challenges along the way. However, with proper planning, education, and a comprehensive approach, these challenges can be overcome. Organizations must remember that implementing a zero trust model is not a one-time task; it requires continuous monitoring and updates to stay effective against evolving cyber threats. By addressing these common challenges and taking a proactive approach, organizations can successfully implement a zero trust model and improve their overall security posture.