In today’s digital landscape, businesses face constant threats from cyber attacks. With the increase in remote work and cloud-based systems, traditional security measures are no longer enough to protect sensitive data and networks. This has led to the rise of Zero Trust Architecture (ZTA) as a more robust and comprehensive security approach. In this blog post, we will explore what Zero Trust Architecture is and how businesses can implement it beyond just IT security.
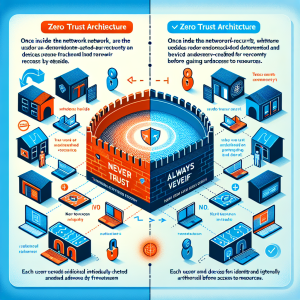
Zero Trust Architecture is a security model that requires strict identity verification and authorization for every user and device attempting to access a network, regardless of whether they are inside or outside the network perimeter. It essentially operates on the principle of “never trust, always verify.” This means that every user and device must prove their identity and meet specific security standards before gaining access to resources.
Traditionally, organizations have relied on a network perimeter-based security approach, where once inside the network, users and devices were trusted by default. However, with the increasing sophistication of cyber attacks, this model has proven to be inadequate. With Zero Trust Architecture, all network traffic is treated as untrusted, and access is granted on a need-to-know basis. This significantly reduces the potential attack surface and limits the impact of any potential breach.

Apart from providing robust security, Zero Trust Architecture also offers several business benefits. One of the most significant advantages is its ability to enable businesses to adopt the latest technologies, such as cloud computing and remote work, without compromising security. With ZTA, businesses can confidently embrace digital transformation and reap its benefits without fear of cyber threats.
Moreover, ZTA also enhances operational efficiency by streamlining access management. With the traditional network perimeter model, managing user access to different resources can be time-consuming and complex. However, with Zero Trust Architecture, access is granted based on predefined policies, making it easier for businesses to manage and track user access.
While Zero Trust Architecture is primarily associated with IT security, its implementation can go beyond just securing networks and data. Businesses can take a business-first approach to implement ZTA and reap its benefits in other areas.
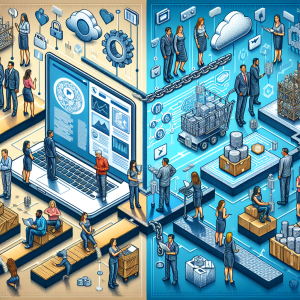
One way to do this is by using ZTA to improve customer experience. With the rise of e-commerce and online services, businesses need to ensure the security of their customers’ data and transactions. By implementing ZTA, businesses can protect customer data and build trust, leading to better customer satisfaction and retention.
Another area where ZTA can be applied is in supply chain management. By implementing ZTA, businesses can secure their supply chain processes, ensuring that only authorized individuals can access and modify data. This reduces the risk of fraud and cyber attacks, ultimately leading to a more secure and efficient supply chain.
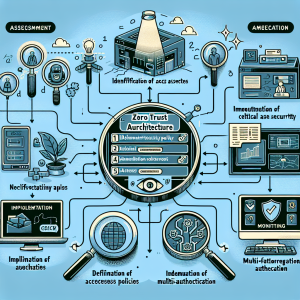
Implementing Zero Trust Architecture involves a series of steps that businesses must follow to ensure its effectiveness. These steps include:
1. Assessment: The first step is to assess the current security infrastructure and identify any gaps or vulnerabilities. This will help businesses understand which areas need improvement and prioritize their implementation efforts.
2. Identify critical assets: Next, businesses must identify their most critical assets, such as sensitive data and systems, and prioritize their security.
3. Define access policies: Once the critical assets have been identified, businesses must define access policies based on the principle of least privilege. This means that users should only have access to the resources necessary to perform their job functions.
4. Implement multi-factor authentication: Multi-factor authentication adds an extra layer of security by requiring users to provide additional verification, such as a one-time password or biometric data, before gaining access.
5. Monitor and review: It is essential to continuously monitor and review access logs and policies to identify any anomalies and make necessary adjustments.

While Zero Trust Architecture offers significant benefits, its implementation can also present some challenges. One of the main challenges is the complexity of implementing ZTA in large organizations with multiple systems and applications. This requires significant resources and expertise, making it challenging for smaller businesses to implement ZTA effectively.
Another challenge is user resistance to the strict access policies and additional authentication measures. This can lead to a decrease in productivity and frustration among employees. To overcome this challenge, businesses must educate their employees on the importance of ZTA and how it benefits both the organization and its employees.
In conclusion, Zero Trust Architecture is not just a security strategy but a business-first approach to ensuring the security and efficiency of modern businesses. By implementing ZTA, businesses can protect their critical assets, improve operational efficiency, and build customer trust. However, its successful implementation requires careful planning and continuous monitoring to stay ahead of evolving cyber threats. With a business-first approach and the right resources, businesses can implement Zero Trust Architecture and reap its benefits beyond just IT security.